Communication Equipment
The Muratec Group, under the direction of management, strives to systematically and continuously improve and enhance information security to protect important information assets such as corporate secrets and employee personal information held by the company, various confidential information and personal information obtained from customers and suppliers, as well as information systems with a significant impact on corporate activities, from information security threats.
To implement, maintain, and improve information security measures while preventing recurring incidents, an Information Security Committee headed by the Chief Information Security Officer has been established to manage all aspects of information security.
The Muratec Group complies with laws, regulations, standards, and contractual obligations with customers, suppliers, and others parties with regard to information security.
We continuously provide training to employees to ensure they acquire the knowledge and skills necessary for information security.
We implement appropriate information security measures to prevent tampering, loss, leakage, unauthorized access, and other damage to information assets. In the event of an incident, we will promptly investigate its cause, prevent further damage, and take measures to prevent recurrence.
We periodically review whether information security is being appropriately operated and maintained, and implement continuous improvement of information security.
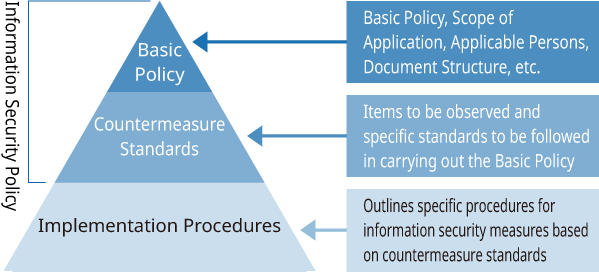
The Muratec Group has established its information security policies—the “Basic Policy Manual” and “Countermeasure Standards Manual”—as the guiding principles and action guidelines for information security measures implemented by the organization and its employees. We establish policies and countermeasure standards based on internationally applicable standards (ISO/IEC 27001/27002:2022) that can be applied to overseas locations, and work to strengthen the foundation of information security using globally common standards.
We have also developed specific implementation procedures based on countermeasure standards, such as the “Information Security Practice Guide” and the “Cloud Security Countermeasure Guidelines.”
Under the leadership of our Group’s Chief Information Security Officer, division heads, headquarters managers, and department heads are appointed to implement various management measures.
The Information Security Committee, chaired by the Chief Information Security Officer, meets regularly to discuss information security measures requiring a company-wide perspective, investigates and reports incidents, and deliberates on recurrence prevention. Within each business division and department, the Information Security Officer takes the lead in implementing information security measures within the department and responds promptly to incidents when they occur.
The Muratec Group implements a combination of advanced malware countermeasures, vulnerability countermeasures for network devices, servers, and PCs, as well as monitoring and analysis between the internet and internal networks to prevent information leaks and business disruptions caused by cyberattacks. We have also established a system that enables recovery even if critical data is lost during emergencies such as disasters, failures, or cyberattacks. This is achieved by backing up critical data using different methods across multiple regional locations.
To evaluate whether information security measures and their implementation are appropriately managed and executed, we conduct annual internal controls audit focused primarily on departments that hold critical information. When issues are identified through internal audits, corrective actions are implemented by each department. Concurrently, we review company-wide information security measures and continuously improve them.
We conduct annual training for all employees to raise awareness of the importance of information security. We also conduct annual training for information security administrators, focusing on deepening their understanding of their roles and objectives while enhancing their technical knowledge and skills. Additionally, we provide training on incidents occurring within the company, methods of cyberattacks that have recently become a social issue, and how to respond to them.